Agentix-Native: A Fundamentally Different Kind of System
The applications that defined the last decade of computing were static and siloed. Cloud-first architecture was the natural design choice for that world. The device was a display. The cloud was the brain.
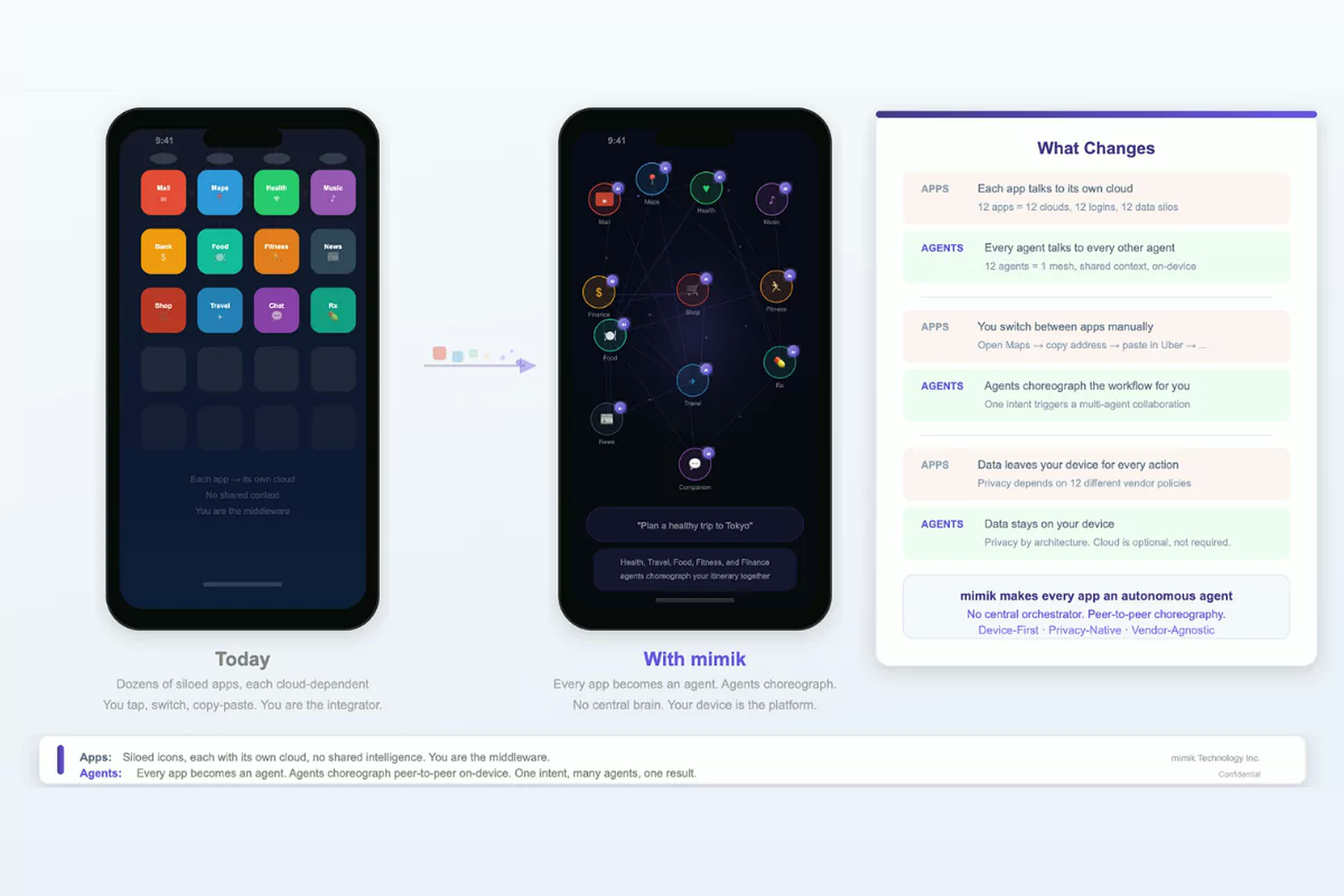
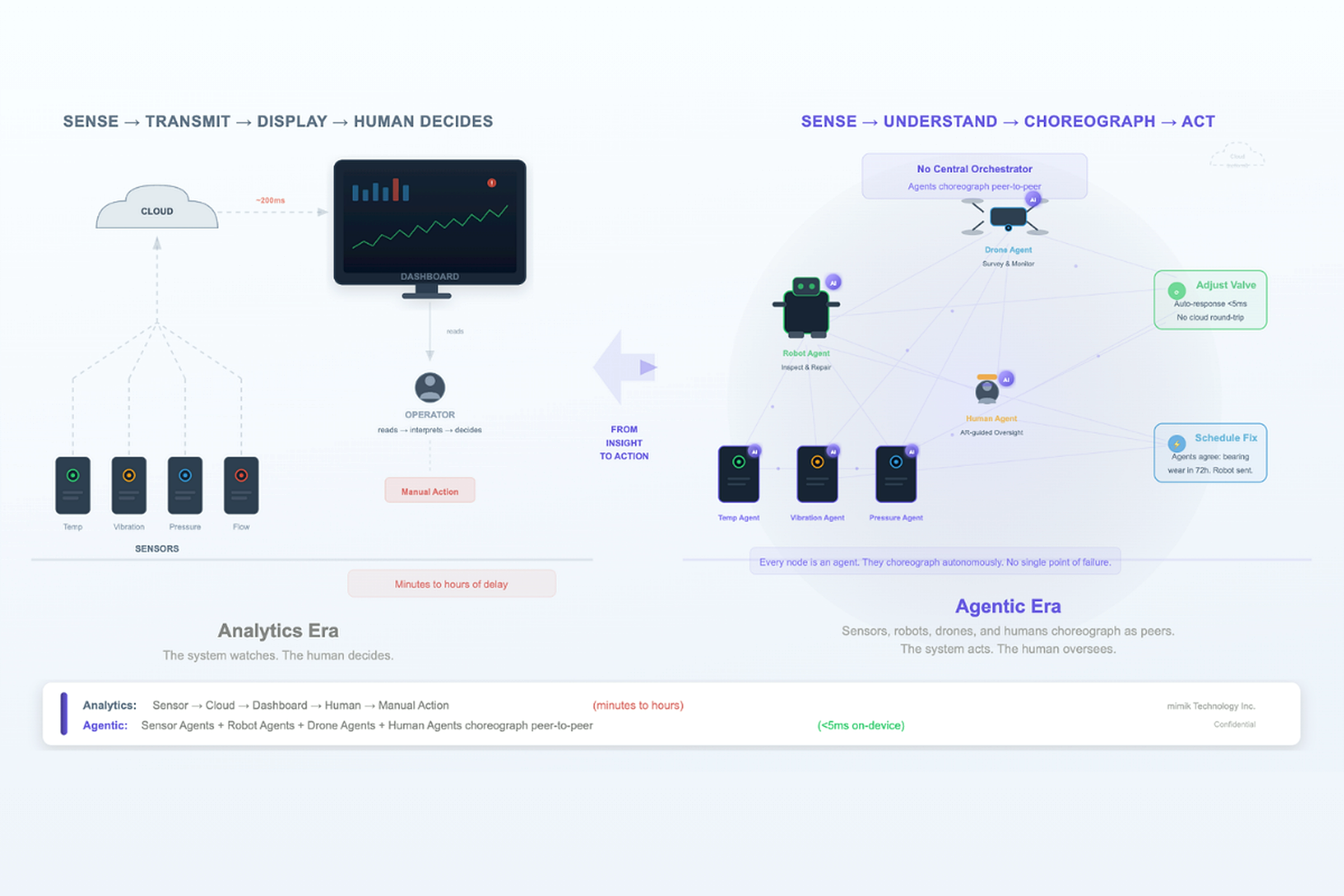
Agentic systems are different in nature, not just in degree. Agents must have autonomy in execution. They must run on devices, at the edge, on premises, and in the cloud simultaneously. They must be able to discover each other dynamically, make decisions in real time, and act directly on data at the point where it is generated. Forcing this model through a cloud-first architecture introduces latency, dependency, and sovereignty gaps that simply did not exist in the static app world.
Yet today, the conversation about sovereign AI is still using the vocabulary and mental model of that older world. In a world where agents think, decide, and act autonomously at the point where data is born, data residency alone does not constitute sovereignty. It is simply the address on the building.
What Sovereignty Actually Means
Sovereignty is the full right and power to govern oneself, make decisions, take action, and persist under one’s own authority, where permission is self-defined and self-governed at the point of execution based on sovereign policies. Four elements must be present simultaneously at the point of execution: authority, control, continuity, and minimum intermediaries on the data path. Remove any one of them and what remains is not sovereignty. It is managed dependence.
Think about how you operate across the full spectrum of your daily activities. In a board meeting you communicate, present, and carry yourself differently than you do with a colleague over lunch, or on a client call, or in a personal conversation. You shift between these contexts fluidly, in real time, sometimes managing several simultaneously. You do not route these decisions through a central authority. You carry your context, your authority, and your boundaries with you and execute instinctively at the point of each interaction. That is sovereignty in execution. Agentix-native systems must be designed to mimic exactly this behavior, deliberately, at every layer, and at machine speed.
Every intermediary on the path between a decision and its execution is a point where sovereignty is conditionally suspended. Any intermediary is a dependency. A chain of intermediaries is a chain of vulnerabilities. This is the condition that current AI architectures routinely violate, including those being marketed as sovereign. The lack of sovereignty in execution is one of the primary reasons AI adoption at scale remains slower than the market expects.
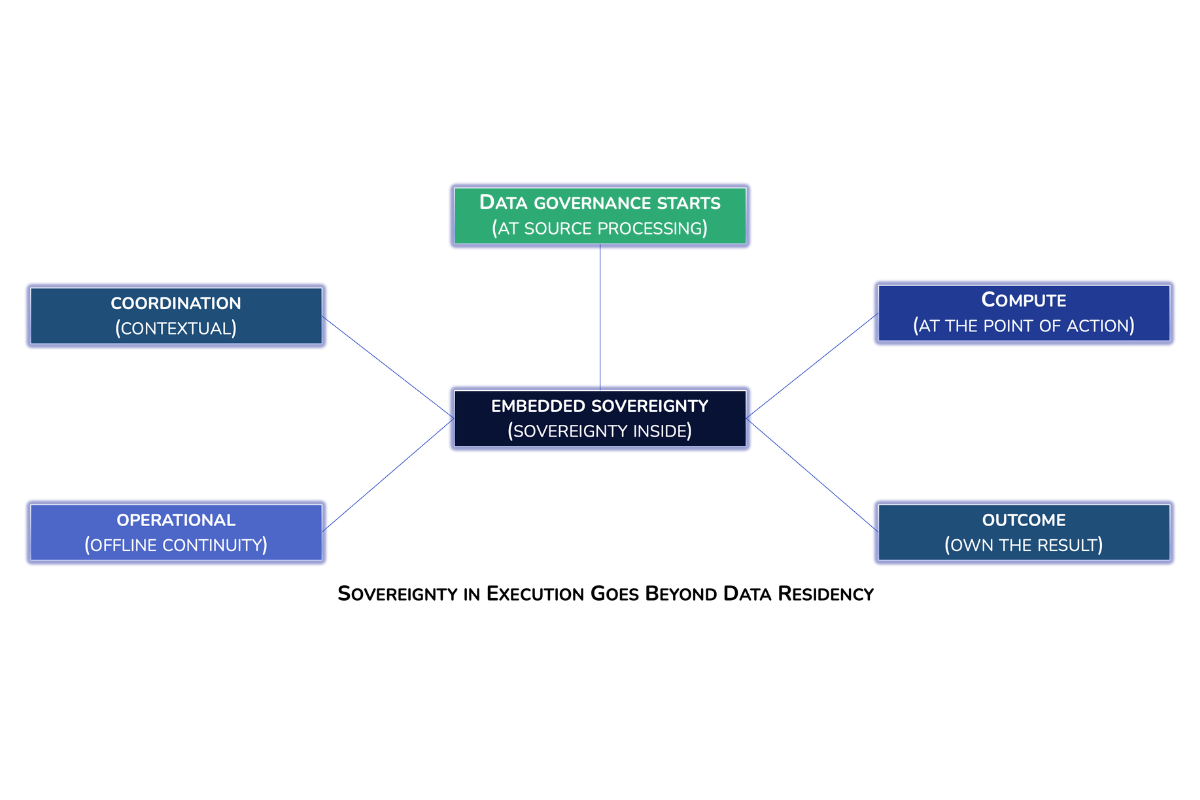
The Five Dimensions of Sovereignty
1. Data Sovereignty: Where Data Governance Starts
Location alone does not tell you who opened the file, who copied it, or who made a decision based on it. It answers one question and leaves four others entirely open.
This means: the agent must be able to process, structure, and enrich data at the point where it is generated, whether on a sensor, a camera, or an industrial machine, and route each scope to the appropriate destinations based on storage and sovereignty policy executed at the source.
2. Compute Sovereignty: Where the Thinking Happens
An AI system that stores data locally but executes inference in an external cloud controls only where the paperwork is filed when the answer comes back. The data has an address. The thinking does not.
This means: the agent must have the autonomy to execute inference at the point of action, within its runtime context and sovereignty policy, without the necessity of a round trip to a remote model or cloud service.
3. Coordination Sovereignty: Who Collaborates and on What Terms
Collaboration is contextual, permission-driven, and scoped to relevance. It must happen directly between the parties who need to work together without routing every exchange through a single gatekeeper who holds everything.
This means: the agent must be able to determine and exercise its authority to collaborate with other agents within its runtime context, dynamically at the point of interaction. This enables autonomous collaboration dynamically choreographed within the bounds of security, access and authorization scope to execute in full operational sovereignty.
4. Operational Sovereignty: The Right to Continue Acting
When the person at the top of the chain is unreachable, the team does not shut down. They operate within their last known mandate until contact is restored. When an AI system loses its cloud connection, it stops. That is not a resilience problem. It is a sovereignty problem.
This means: the agent must be able to determine and exercise its authority to collaborate with other agents within its runtime context, dynamically at the point of interaction, carrying the ontological context it needs to act without reaching back to a central system for meaning. This enables autonomous collaboration dynamically choreographed within the bounds of security, access and authorization scope to execute in full operational sovereignty.
5. Outcome Sovereignty: Who Owns the Result
If the signature on a deliverable must happen on someone else’s platform, using someone else’s ledger, the outcome has a dependency built into it regardless of how the work leading up to it was conducted.
This means: the agent must be able to settle the results of its actions, record outcomes, and maintain an audit trail with full observability of every execution, operation, and interaction from the source, within its own runtime environment, under the organization’s full control.
Embedded Sovereignty: Where all 5 Dimensions Converge
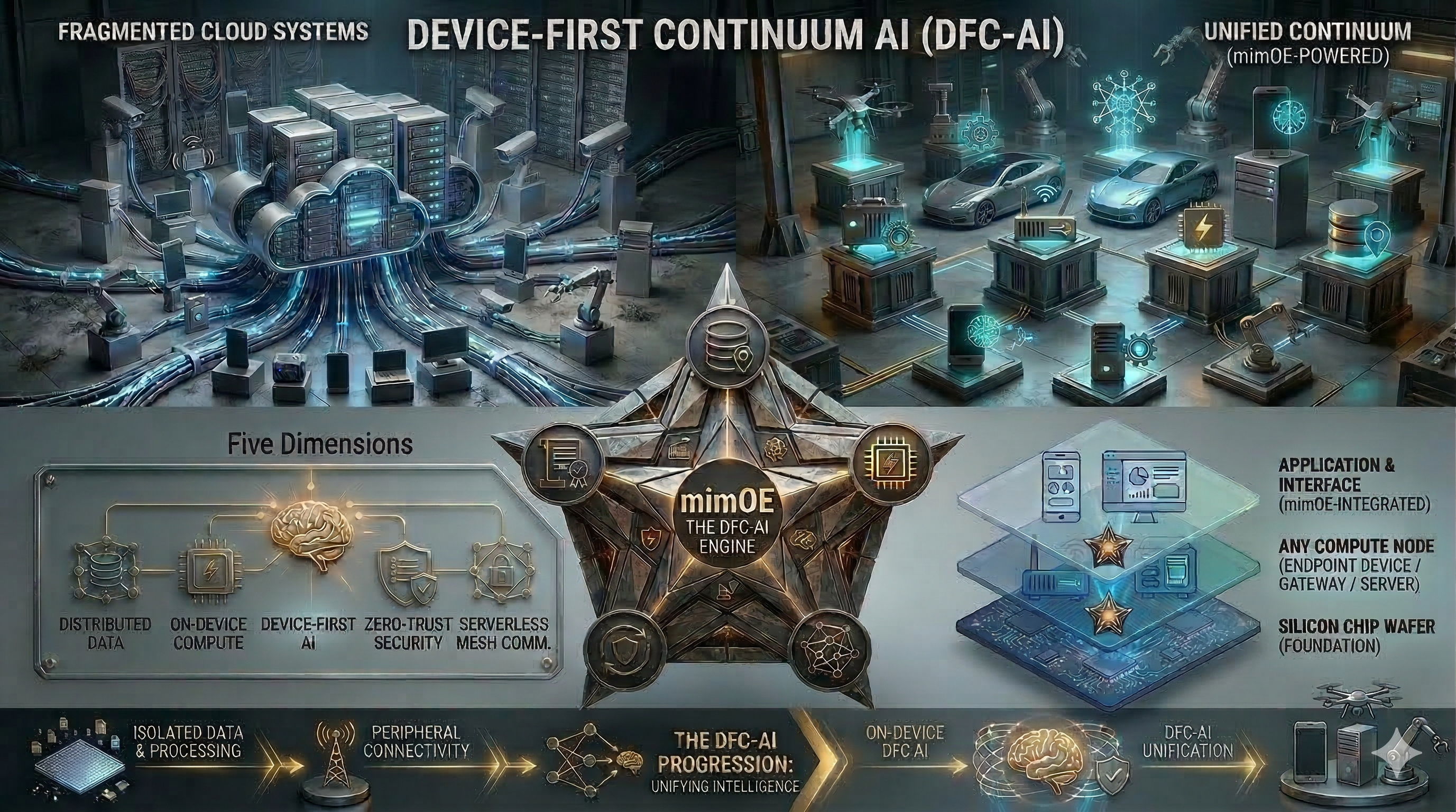
Embedded Sovereignty is a dedicated execution layer present at the point of origin, delivered in three forms:
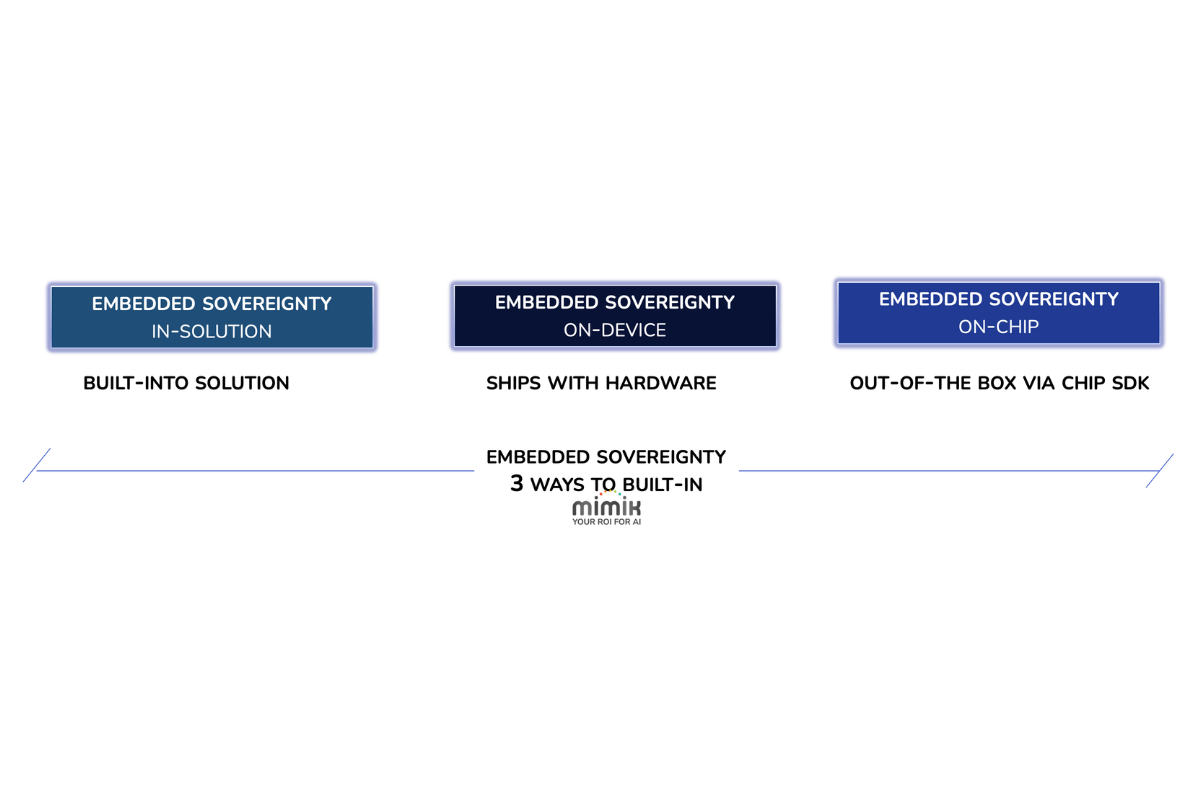
as part of an agentix solution or application as Sovereignty-in-solution, pre-integrated on a device as Sovereignty-on-Device, or embedded at the chip level as Sovereignty-on-Chip. The closer it is to the chip, the faster the path to production for the entire ecosystem: device vendors, developers, and enterprises alike. Without it, each of the five dimensions requires a separate implementation effort. Data residency requires infrastructure decisions. Compute sovereignty requires on-device inference capability. Coordination sovereignty requires a distributed agent runtime. Operational sovereignty requires offline-first architecture. Outcome sovereignty requires on-device settlement capability.
Addressed individually, each is a project. Addressed sequentially, they compound into years of engineering debt. From the moment a system with Embedded Sovereignty powers on, connected or not, all five dimensions are already satisfied. That is the difference between sovereignty as a destination and sovereignty as a design principle. That design principle is also what distinguishes Embedded Sovereignty from an operating system. An operating system is passive by design. It manages resources and waits for instructions. Agents do not wait. They collaborate with other agents in dynamic workflows. Operating based on the principles of follow, observe, respond, and learn, they discover, decide, coordinate, and act proactively based on context, authority, and sovereign policy. What they require is a Sovereign Execution System, one that is device-first by design, as autonomous and context-aware as the agents running within it, and capable of operating across the full compute continuum from the chip to the cloud.
For the enterprise, Embedded Sovereignty is not an infrastructure decision. It is the difference between AI that operates under your authority and AI that operates under someone else’s.
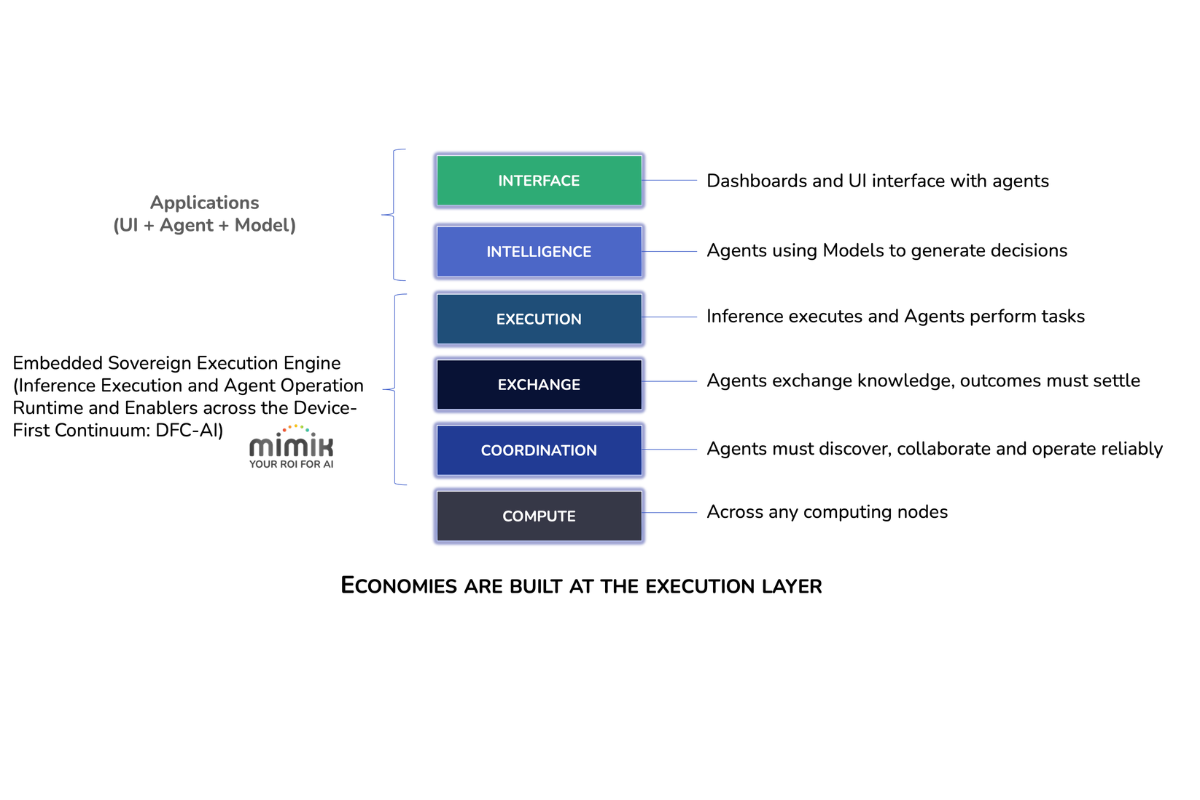
Without it, every jurisdiction becomes a re-engineering project, every cloud dependency becomes a point of operational risk, and every sovereignty gap accumulates into compliance and liability exposure. With it, the organization deploys once, governs from the point of execution, and retains full control across every context in which its agents operate. For device vendors and OEMs, every device that ships becomes a production-ready sovereign node out of the box. For developers, the execution environment travels with the agent across any hardware, any OS, and any connectivity state.
This is not a future capability. mimik delivers Embedded Sovereignty as a production-ready platform, available today at the solution, device, and chip level.